Reclaim Your Digital Privacy: A Step-by-Step Guide to Spring Cleaning Your Online Data
Introduction
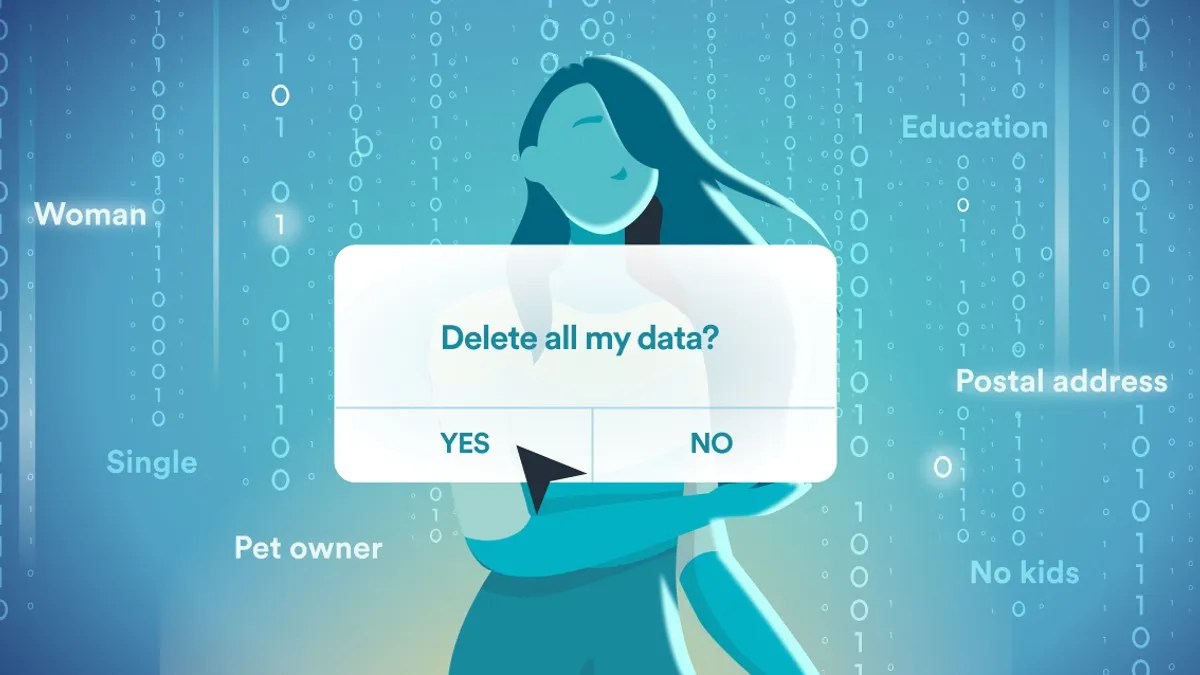
As the last snow melts and the days grow longer, we instinctively reach for the mop, the broom, and the donation box. Spring cleaning feels good—it clears the air, literally and figuratively. Yet, while we scrub our homes from top to bottom, we often ignore a far more cluttered space: our digital lives. Your home address, phone number, date of birth, financial history, and even your shopping habits are scattered across the web, hoarded by invisible data brokers who buy, sell, and trade your personal information without your permission. It’s time for a digital spring cleaning. This guide will walk you through a thorough, step-by-step process to sweep away your digital clutter and reclaim your privacy—effortlessly, with help from Incogni. By the end, you’ll know exactly how to scrub your data from broker databases and keep it that way.
What You Need
- A computer or smartphone with internet access
- Your primary email address(es) that you use for online accounts
- A list of old, unused accounts (social media, forums, shopping, etc.)
- Access to your password manager (if you use one)
- An Incogni subscription (get an exclusive 55% discount for 9to5Mac readers using the link below)
- About 60–90 minutes of uninterrupted time
- A secure browsing session (use a private window if possible)
Step-by-Step Instructions
Step 1: Audit Your Digital Footprint
Before you clean, you need to know what’s out there. Start by searching yourself on major search engines like Google, Bing, and DuckDuckGo. Use your full name, nickname, email address, and phone number. Note any public records, social media profiles, old forum posts, or data broker sites (like Whitepages, Spokeo, or MyLife). Also check your email inbox for newsletters, account confirmations, and forgotten subscriptions. This audit takes 15–20 minutes but gives you a clear picture of what needs to go.
Step 2: Delete Unused Online Accounts
Old accounts are low-hanging fruit for data brokers. They collect the information you once volunteered and resell it. Go through your password manager or browser autofill list for sites you haven’t used in over a year. Log in, navigate to account settings, and look for a delete account option (often under Privacy or Security). For sites that only allow deactivation, use a service like Incogni to force removal later. Delete at least 10 accounts—aim for every account that holds your real data. Pro tip: Use Have I Been Pwned to check if any of these accounts were part of a data breach.
Step 3: Opt Out of Data Brokers Manually (or Automate with Incogni)
Data brokers are the heart of the problem. You can opt out individually from the biggest brokers (like Acxiom, Oracle, Epsilon) by visiting their opt-out pages, submitting a request, and verifying your email. But there are hundreds of brokers—this manual process can take hours. Instead, use Incogni, a tool that automatically finds and removes your personal information from over 100 data broker databases. It sends removal requests on your behalf and tracks progress. To start, create an Incogni account, provide your name, email, and phone number (the tool needs these to target your data), and let it run. 9to5Mac readers can save 55% right now. After a week, check your dashboard—most removals happen within 7–14 days.
Step 4: Clean Up Your Social Media Profiles
Social media platforms are data gold mines. Go through each platform you use (Facebook, Instagram, Twitter, LinkedIn, etc.) and remove personal details that aren’t necessary. Turn off location tagging, set posts to “Friends Only” or “Private,” and delete old photos that reveal your home, workplace, or family. On Facebook, download your data first (just in case), then use the “Manage Activity” tool to bulk-delete old posts. On LinkedIn, remove your full address and phone number from the profile. Key: Set your profile to be as private as possible—only share what’s required for the platform to function.

Step 5: Lock Down Your Email and Devices
Your email is the master key to your digital life. Enable two-factor authentication (2FA) on your primary email account. Also turn on 2FA for your phone carrier account (to prevent SIM swapping) and your password manager. Next, update your passwords—use a unique, strong password for every account. If you reuse passwords, reset them now. Finally, review app permissions on your phone and laptop: revoke access for apps you no longer use. For example, old games with location access or a flashlight app that wants your contacts. This step secures your digital perimeter post-cleaning.
Step 6: Set Up Ongoing Monitoring
Digital spring cleaning isn’t a one-time event—spiders and brokers will try to collect your data again. Use Incogni’s continuous monitoring feature that automatically re-scans broker databases every few months and re-submits removal requests if your data reappears. Also subscribe to a credit monitoring service (like Credit Karma or your bank’s offering) to catch identity theft early. Finally, bookmark this guide and set a reminder for six months from now to repeat Steps 1 and 2. With Incogni handling the heavy lifting, maintenance takes only 10 minutes per quarter.
Tips for Success
- Start with the worst offenders: If you’re short on time, focus on data brokers (Step 3) first—they sell your info to everyone. Incogni is worth the investment.
- Use a temporary email for sign-ups: For future account creations, use a temporary email address (like from Guerrilla Mail) to avoid polluting your real inbox.
- Don’t forget Google and Apple accounts: Log into your Google Account’s “Data & Privacy” section and turn off ad personalization, location history, and YouTube history. Do the same for Apple ID under “Privacy & Security.”
- Beware of phishing during cleanup: Data brokers might send fake opt-out emails. Always verify through Incogni or official opt-out pages.
- Combine with physical security: Shred old credit card offers and bank statements that contain personal data—digital cleanup works best when physical documents are also secured.
- Share only what’s necessary: Going forward, treat your personal information like cash—don’t hand it out without a good reason.